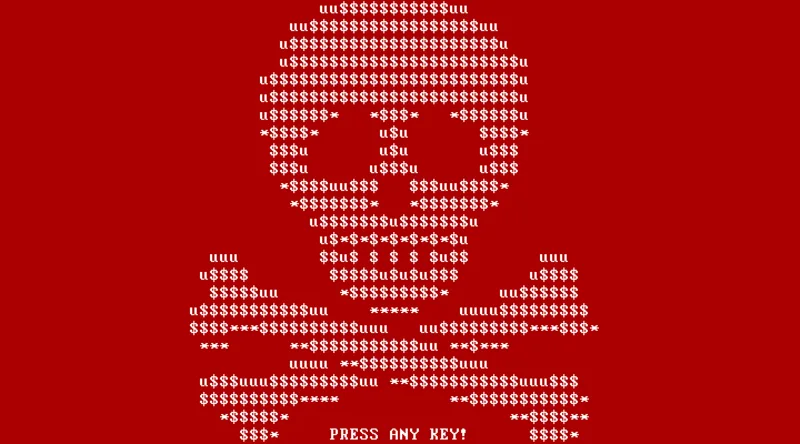
NotPetya Wiper Disguised as Ransomware Causes $10 Billion in Global Damage
What happened
NotPetya, a destructive wiper disguised as ransomware, spread via a trojanised Ukrainian accounting software update and EternalBlue. It destroyed systems at Maersk (shipping), Merck (pharma), FedEx, and hundreds of other companies. With no real decryption mechanism, victims could not recover data — total damage exceeded $10 billion.[1]
What went wrong
The initial infection vector was a software supply chain compromise of MeDoc, widely used Ukrainian accounting software. Once inside corporate networks, NotPetya spread rapidly because of flat network architectures and legitimate admin credential reuse via Mimikatz.[1]
Lesson learned
Cyber weapons do not respect borders — a nation-state operation against Ukraine became the costliest cyberattack in history for Western multinationals. Offline backups, network segmentation, and software supply chain verification are existential requirements, not optional hardening.
Sources
- [1]
External links can go dark — pages move, paywalls appear, domains expire. Every source above includes a Wayback Machine snapshot link as a fallback. All citations are best-effort research; if a source contradicts our summary, the primary source takes precedence.